HMV Helium Summary
2026-03-27
2026-03-27122 Words
Scope
- Name: Helium
- Diffculty: (2/10)
- OS: Linux
- IP: helium.hmv(192.168.56.107)
Foothold
First, I access the homepage of the web service.
❯ curl http://helium.hmv/ <title>RELAX</title> <!doctype html> <html lang="en"> <!-- Please paul, stop uploading weird .wav files using /upload_sound --> <head> <style> body { background-image: url('screen-1.jpg'); background-repeat: no-repeat; background-attachment: fixed; background-size: 100% 100%; } </style> <link href="bootstrap.min.css" rel="stylesheet"> <meta name="viewport" content="width=device-width, initial-scale=1"> </head> <body> <audio src="relax.wav" preload="auto loop" controls></audio> </body>%
I get some key points from that:
- There is a user named
paul. - There are maybe some
.wavfiles out there which uploaded via/upload_soundendpoint. - I could download the
relax.wavandscreen-1.jpgfirst.
I get nothing interesting from that two files, so I decide to enumerate the directory of the web service.
❯ feroxbuster -u http://helium.hmv/ -w /usr/share/wordlists/dirb/common.txt -x php,html,txt,js ___ ___ __ __ __ __ __ ___ |__ |__ |__) |__) | / ` / \ \_/ | | \ |__ | |___ | \ | \ | \__, \__/ / \ | |__/ |___ by Ben "epi" Risher 🤓 ver: 2.13.1 ───────────────────────────┬────────────────────── 🎯 Target Url │ http://helium.hmv/ 🚩 In-Scope Url │ helium.hmv 🚀 Threads │ 50 📖 Wordlist │ /usr/share/wordlists/dirb/common.txt 👌 Status Codes │ All Status Codes! 💥 Timeout (secs) │ 7 🦡 User-Agent │ feroxbuster/2.13.1 💉 Config File │ /home/curtain/.config/feroxbuster/ferox-config.toml 🔎 Extract Links │ true 💲 Extensions │ [php, html, txt, js] 🏁 HTTP methods │ [GET] 🔃 Recursion Depth │ 4 ───────────────────────────┴────────────────────── 🏁 Press [ENTER] to use the Scan Management Menu™ ────────────────────────────────────────────────── 404 GET 7l 12w 169c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter 200 GET 1l 1w 23c http://helium.hmv/bootstrap.min.css 200 GET 22l 46w 530c http://helium.hmv/ 200 GET 22l 46w 530c http://helium.hmv/index.html [####################] - 2s 23075/23075 0s found:3 errors:0 [####################] - 1s 23070/23070 24806/s http://helium.hmv/ ❯ curl http://helium.hmv/bootstrap.min.css /yay/mysecretsound.wav
Yeah, the weird wav file stands out! Then I get the spectrogram by ffmpeg.
ffmpeg -i mysecretsound.wav -lavfi showspectrumpic=s=1900x1028 spectrogram.avif
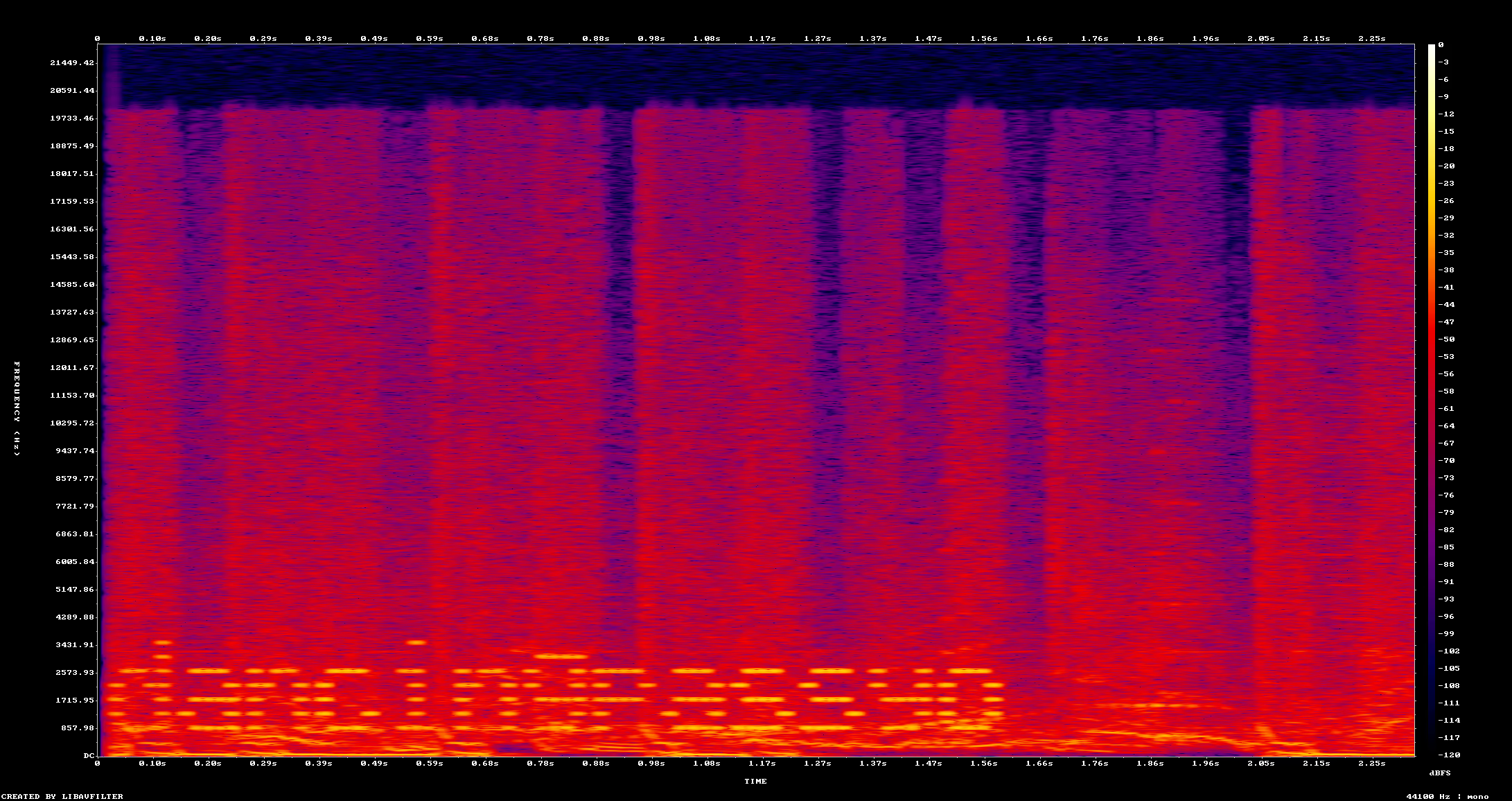
Then I login the system with user paul and this password.
Privilege Escalation
This step is very straightforward, cause sudo rule is what I need.
paul@helium:~$ sudo -l
Matching Defaults entries for paul on helium:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User paul may run the following commands on helium:
(ALL : ALL) NOPASSWD: /usr/bin/ln
And GTFBins - ln helps me to get root shell.